Contents
1. Overview
2. Getting Started
3. SQL Instance Connection
3.1 Single Instance
3.2 Multiple Instances
4. Security Checks
4.1 Server-Level Accesses
4.1.1 Logins – Server Role Associations
4.2 Surface Area
4.2.1 Ad Hoc Distributed Queries
4.2.2 CLR Enabled
4.2.3 Cross DB Ownership Chaining
4.2.4 Database Mail XPs
4.2.5 Ole Automation Procedures
4.2.6 Remote Access
4.2.7 Remote Admin Connections
4.2.8 Scan for Startup Procs
4.2.9 SQL Mail XPs
4.2.10 Trustworthy
4.2.11 SA Account Status
4.2.12 xp_cmdshell
4.3 Authentication & Authorization
4.3.1 Server Authentication Mode
4.3.2 Guest User
4.3.3 Orphaned Users
4.3.4 Public Database Role
4.4 Password Policies
4.4.1 Password Expiration
4.4.2 Password Policy
4.4.3 Checks for SA (password expiration and policy)
4.5 Auditing
4.5.1 Login Auditing Setting
4.5.2 Default Trace Enabled Setting
4.5.3 Today’s List of Failed Logins
4.5.4 Last Password Changes
4.6 Miscellaneous
4.6.1 CLR Assembly Permission Set
4.6.2 Transparent Data Encryption
4.6.3 SQL Server Version
4.6.4 Service Pack Info
4.7 Advanced
4.7.1 Database Engine Service Account
4.7.2 SQL Agent Service Account
4.7.3 Credentials Check (sa:sa)
4.7.4 Credentials Check (user:user)
4.7.5 Latest DB Backup Times
4.7.6 BUILTIN\Administrators Access
5. Report
5.1 Display Options
5.2 Export Options
5.3 View Report in Report Viewer
5.4 Suggest Remediation Scripts
6. Security Report Viewer
6.1 Display Options
6.2 Export Options
7. Tools
7.1 Customize
7.2 Options
8. History
8.1 View Older Reports
8.2 Clear Report History
9. Extras
9.1 Connected Instance(s) Information
9.2 Clear List of Recently Connected Instances
10. Special Topics
10.1 Available Editions and Feature Comparison
10.2 Why Upgrading to the Enterprise Edition?
10.3 How Should You Use DBA Security Advisor
10.4 Purchasing and Activating the Enterprise Edition
Appendix A
1. Overview
DBA Security Advisor is a powerful security tool that can assess single or multiple SQL Server instances against a rich set of security checks and provide recommendations as well as remediation methods and scripts. All the security checks and recommendations are based on proven security best practices which can help you secure your SQL Server instances and thus protect your data more efficiently.
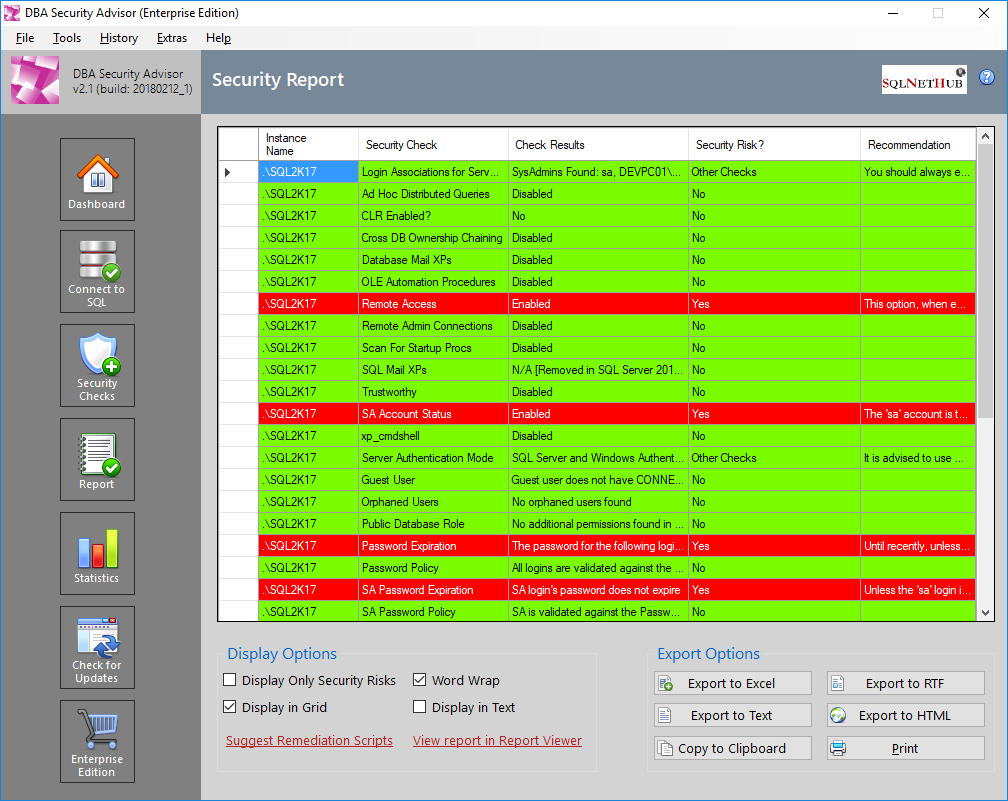
Figure 1.1: Embedded Report Viewer in DBA Security Advisor.
2. Getting Started
Note: It is advised that DBA Security Advisor is only used by experienced Database Administrators or Certified SQL Server technicians. Changing the settings/options of SQL Instance(s) requires the knowledge of how each setting can affect the operation of SQL Server and especially the operation of the supported applications whose databases are hosted in the SQL Server instance.
Having said the above, let’s see how you can get started with DBA Security Advisor via a simple example.
Note that this example assumes that you are using the Enterprise Edition of the tool where all security checks and other features are available.
This example features a single SQL Server instance that will be assessed against specific security checks. The instance name is ‘.\SQL2K14’.
The first step, after starting DBA Security Advisor, is to connect to the above SQL Server instance. This can be done from the SQL Instance Connection page:
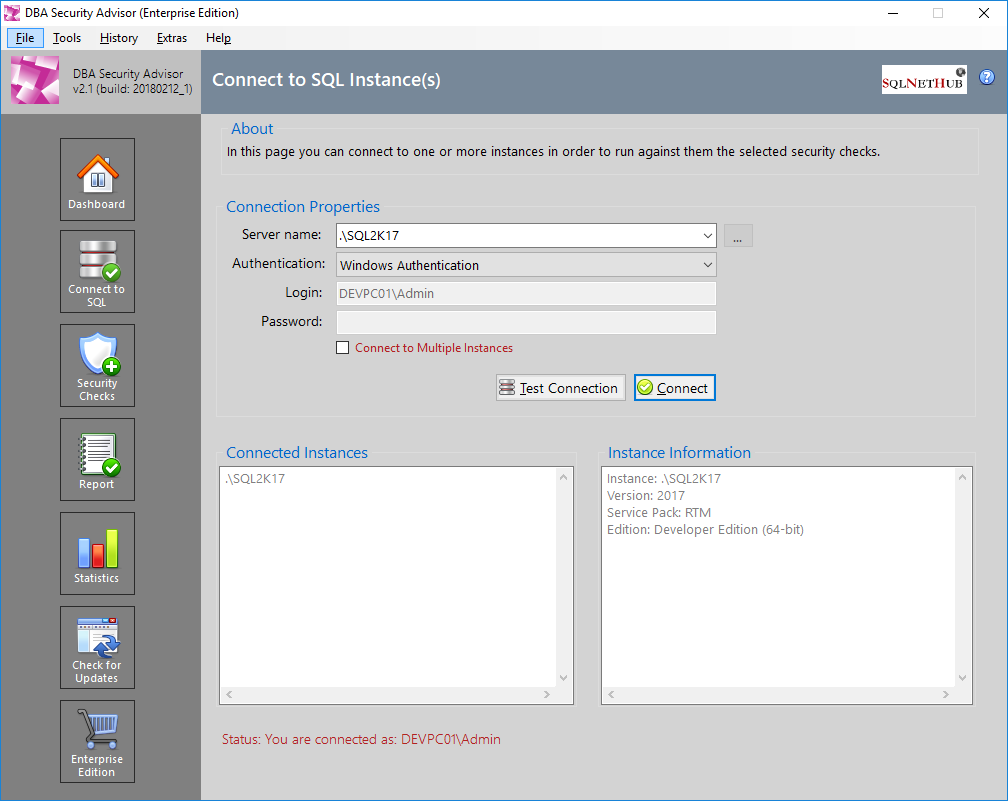
Figure 2.1: Connecting to SQL Server Instance ‘.\SQL2K17’.
The second step is to select the security checks against which the specified SQL Server instance will be assessed. For this example, we will just select the following security checks:
- CLR Enabled (from category: Surface Area)
- Ole Automation Procedures (from category: Surface Area)
- xp_cmdshell (from category: Surface Area)
- CLR Assembly Permission Set (from category: Miscellaneous)
- Credentials Check: user:user (from category: Advanced)
- Latest DB Backup Times (from category: Advanced)
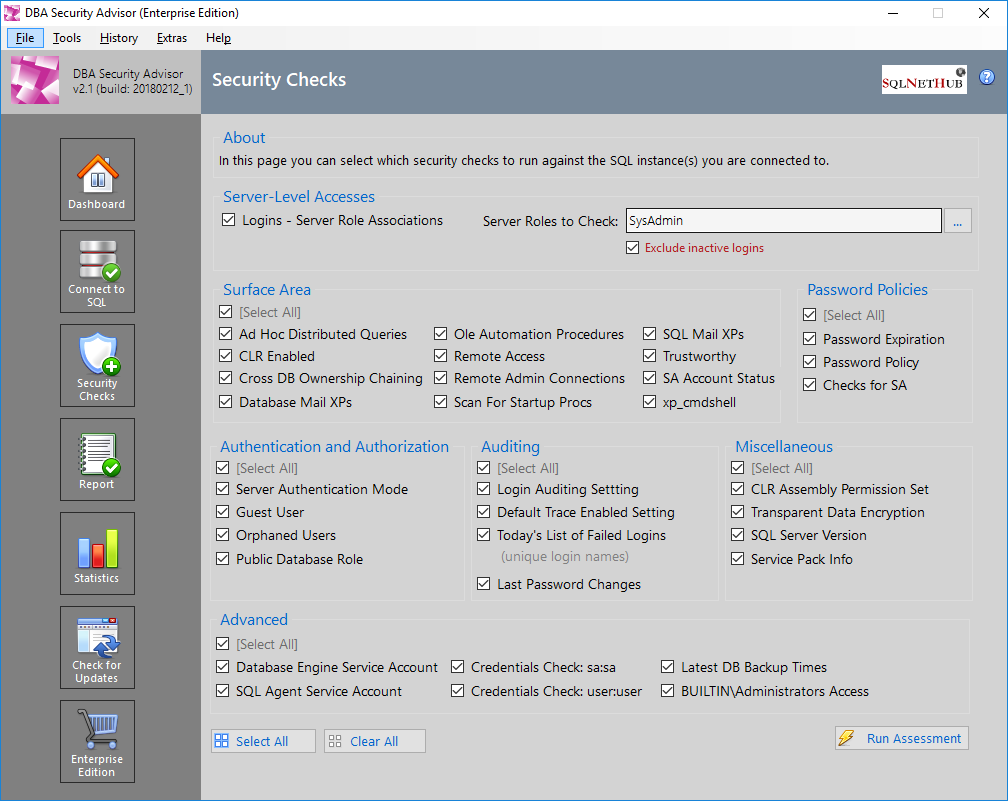
Figure 2.2: Selecting the Security Checks for the Current Assessment Session for SQL Server Instance ‘.\SQL2K17’.
Then, as a third step, we run the checks and we get the report:
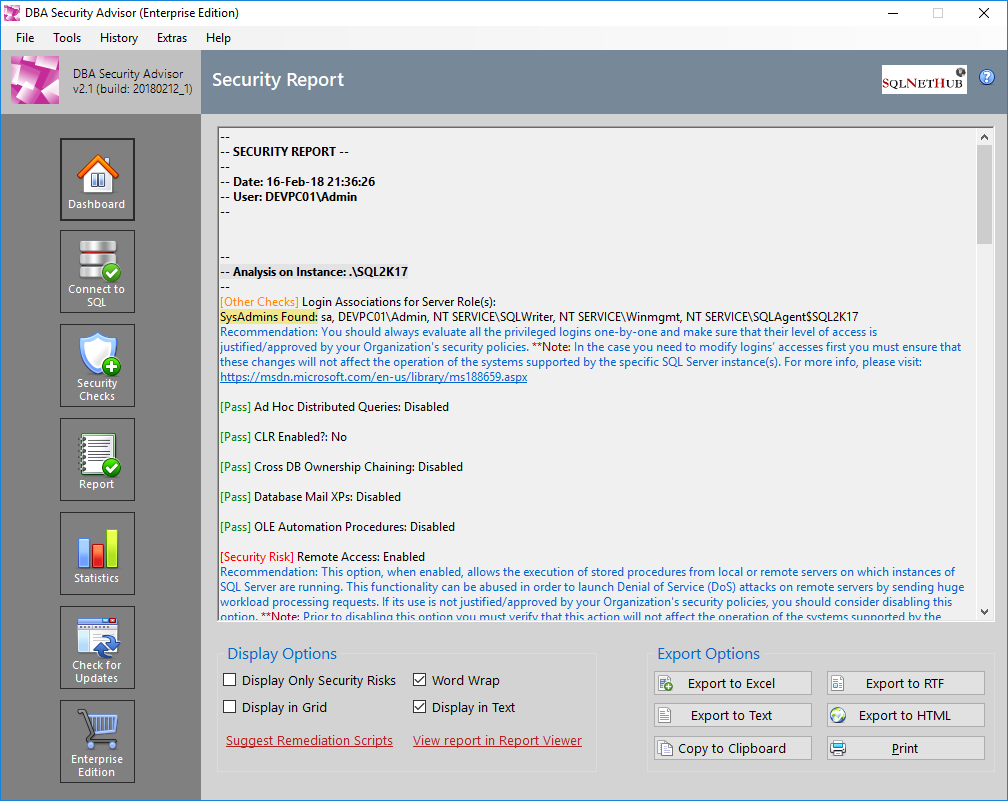
Figure 2.3: The Generated Report for the Current Assessment Session of SQL Server Instance ‘.\SQL2K17’.
As you can see, for the selected security checks, there is only one ‘scored’ detected security risk, that is having CLR Enabled, and one ‘Other Check’ finding that has to do with some databases that have not been recently backed up.
The fourth and more important step, is to analyze the report and decide the actions to be taken. The first action item to note down is to check why a backup was not taken for the reported databases and fix the process that backs up the databases.
The second action is to proceed with the Remediation Scripts suggestion in order to see how you can remediate the scored security risk that is the CLR Enabled finding. To this end, we now click on the ‘Suggest Remediation Scripts’ link and we see the items flagged as ‘Security Risk’ along with the recommendation and remediation script or method. In this case, only the ‘CLR Enabled’ option has been marked as a potential security risk and needs to be further investigated and handled.
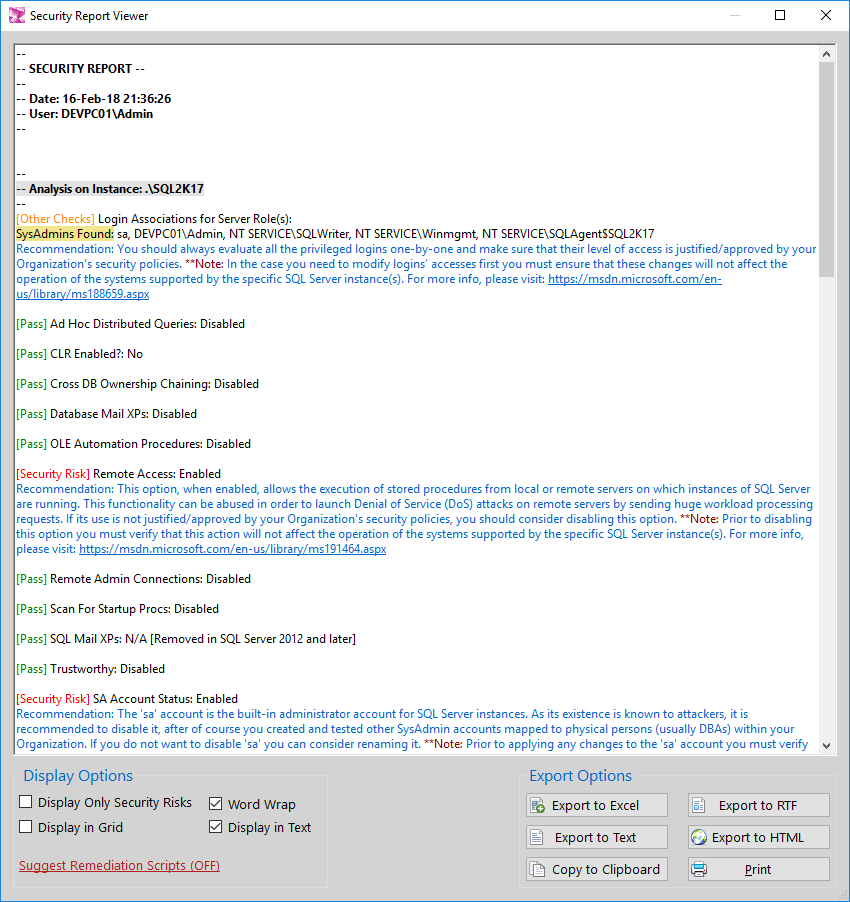
Figure 2.4: View in Security report Viewer Recommendations and Remediation Scripts/Methods for Items Flagged as Security Risks.
As you can read in the recommendation, you need to investigate if having the ‘CLR Enabled’ enabled in the specific SQL Server instance is justified and approved by your organization. If its use is approved, then you need to ensure that the CLR Assembly Permission Set is set to ‘SAFE’ and if so, then no other action is required. If, however the ‘CLR Enabled’ option is not required by business and neither is approved by your Organization’s Security policies, then after you ensure that by disabling this feature will not affect the operation of any application whose database is hosted on the specific SQL Server instance, you should consider disabling this feature using the provided remediation script.
Note: At this point it is important to note that even though some configuration options in your SQL Server instances could be reported as potential security risks, you should consider these findings as indicative because it is the business needs and your organization’s security policies and procedures that define whether an option should be enabled or not and how should it be configured.
3. SQL Instance Connection
Via the SQL Instance Connection page, you can connect to the SQL Server instance(s) against which you will run the security assessment. You can connect by either using Windows Authentication or a SQL Server Login (username/password). In the Free 7-Day Trial Version of DBA Security Advisor, you can connect to and assess a single instance at-a-time. In the Enterprise Edition, you can connect to and assess multiple instances at the same time. Upon connecting to the SQL Server instance(s), you will be presented with basic information about them such as: instance name, version, service pack installed and edition.
Note: DBA Security Advisor supports SQL Server 2005 or later and you need to connect as SysAdmin in order to be able to use the tool.
3.1 Single Instance
The below screenshot illustrates an example of DBA Security Advisor connected to a single SQL Server instance.
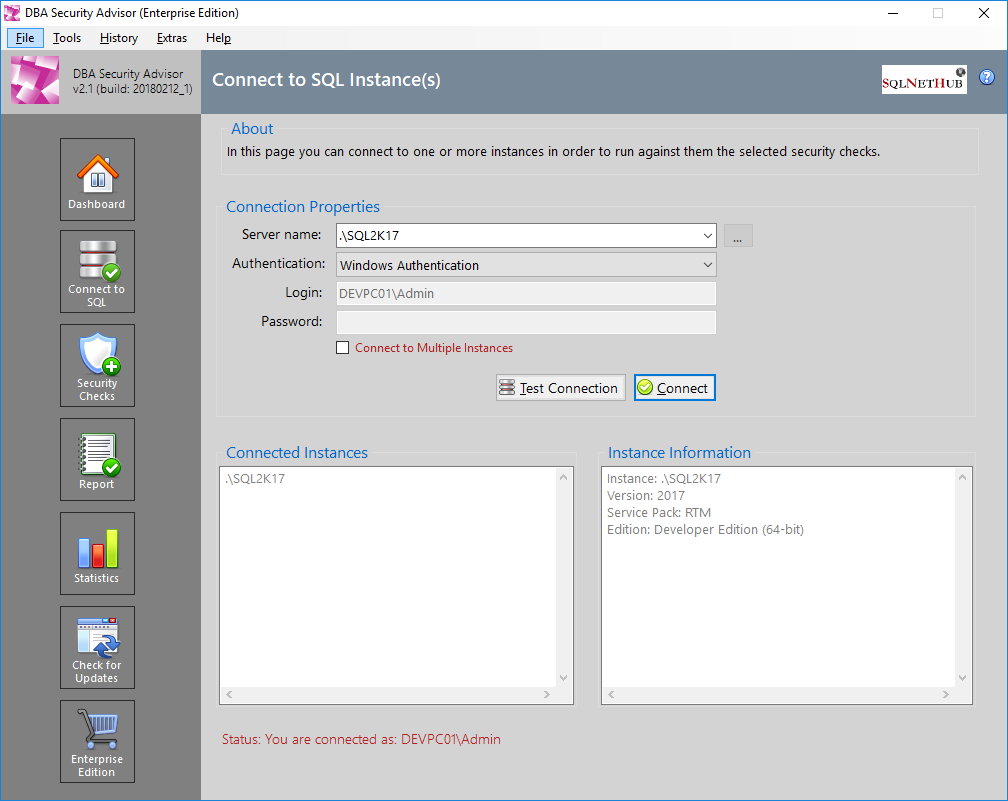
Figure 3.1: SQL Instance Connection Dialog: Single Instance.
3.2 Multiple Instances
The below screenshot illustrates an example of DBA Security Advisor connected to multiple SQL Server instances using the Enterprise Edition.
image
Figure 3.2: SQL Instance(s) Connection Dialog: Multiple Instances.
If you are using Enterprise Edition, in order to connect to multiple SQL Server instances you just need to click on the checkbox “Connect to Multiple Instances” on the SQL Instance Connection Page and a dialog will be presented in which you can specify one instance at a line like the below example:
image
Figure 3.3: SQL Instance(s) Connection Dialog: Specify Multiple Instances.
Additionally, after you connect to multiple instances, in case you want to add or remove instances from your selection and reconnect, you can do so by clicking on the button “…” which can be found to the right of the “Server name” box. After your modification is completed, by clicking on the “Connect” button again, you will connect to the new list of SQL instances.
4. Security Checks
DBA Security Advisor provides a rich set of security checks based on proven SQL Server security best practices. In the Enterprise Edition of the current version of DBA Security Advisor, there are available more than 30 security checks that are organized into 7 categories. These categories are:
Server-Level Accesses
Surface Area
Authentication and Authorization
Password Policies
Auditing
Miscellaneous
Advanced
Below you can find more information about each category and its security checks.
Note: In the Free 7-Day Trial Version of DBA Security Advisor, only the following categories are available: Server-Level Accesses, Surface Area, Authentication and Authorization and Password Policies.
4.1 Server-Level Accesses
This category features security checks that have to do with server-level accesses, that is server roles.
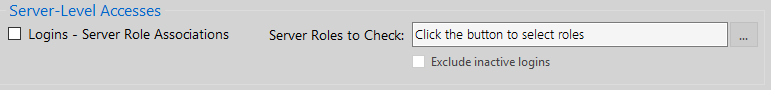
Figure 4.1: ‘Server-Level Accesses’ Security Check Group.
4.1.1 Logins – Server Role Associations
This security check allows you to select a set of SQL Server roles and checks which users are assigned these roles. For example, you can choose to see all the ‘SysAdmins’ on the selected instances.
image
Figure 4.2: Logins – Server Role Associations Check: Select Server Roles.
4.2 Surface Area
This category features a set of checks that have to do with SQL Server’s surface area configuration.
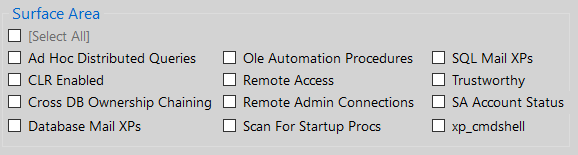
Figure 4.3: ‘Surface Area’ Security Check Group.
4.2.1 Ad Hoc Distributed Queries
This check checks if the ‘Ad Hoc Distributed Queries’ Server Configuration Option is enabled or not.
4.2.2 CLR Enabled
This check checks if the ‘clr enabled’ Server Configuration Option is enabled or not.
4.2.3 Cross DB Ownership Chaining
This check checks if the ‘cross db ownership chaining’ Server Configuration Option is enabled or not.
4.2.4 Database Mail XPs
This check checks if the ‘Database Mail XPs’ Server Configuration Option is enabled or not.
4.2.5 Ole Automation Procedures
This check checks if the ‘Ole Automation Procedures’ Server Configuration Option is enabled or not.
4.2.6 Remote Access
This check checks if the ‘remote access’ Server Configuration Option is enabled or not.
4.2.7 Remote Admin Connections
This check checks if the ‘remote admin connections’ Server Configuration Option is enabled or not.
4.2.8 Scan for Startup Procs
This check checks if the ‘scan for startup procs’ Server Configuration Option is enabled or not.
4.2.9 SQL Mail XPs
This check checks if the ‘SQL Mail XPs’ Server Configuration Option is enabled or not. Note that ‘SQL Mail XPs’ option was removed in SQL Server 2012 and later.
4.2.10 Trustworthy
This check checks if the ‘Trustworthy’ database option is enabled and if yes, for which tables.
4.2.11 SA Account Status
This check checks if the ‘sa’ built-in SQL Server administrator is enabled.
4.2.12 xp_cmdshell
This check checks if the ‘xp_cmdshell’ Server Configuration Option is enabled or not.
4.3 Authentication & Authorization
This category features a set of checks that have to do with SQL Server’s authentication and authorization functions.
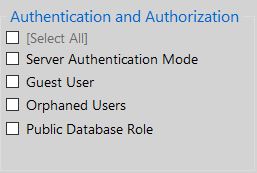
Figure 4.4: ‘Authentication and Authorization’ Security Check Group.
4.3.1 Server Authentication Mode
This check checks the SQL Server authentication mode if it is set to ‘Windows Authentication’ or ‘SQL Server and Windows Authentication’.
4.3.2 Guest User
This check checks if guest user has ‘CONNECT’ permissions to any user database.
4.3.3 Orphaned Users
This check checks if there are any orphaned users in any database (it excludes the cases where the database is contained).
4.3.4 Public Database Role
This check checks if the public database role, besides the default-given permissions, has any additional user-given permissions on the databases.
4.4 Password Policies
This category contains checks that have to do with password expiration and password policy enforcement for SQL Server logins. It also features the same checks just for the ‘sa’ login.
Note: The first two checks check all users, including the ‘sa’ login. However, in case you just want to check the ‘sa’ login, you can use the dedicated check that exists for this purpose.
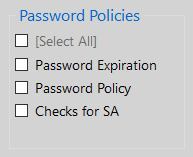
Figure 4.5: ‘Password Policies’ Security Check Group.
4.4.1 Password Expiration
This check checks which SQL logins, if any, have passwords that do not expire and reports them.
4.4.2 Password Policy
This check checks for which SQL logins, if any, the password policy is not enforced and reports them.
4.4.3 Checks for SA (password expiration and policy)
This check checks if the ‘sa’ login’s password does not expire as well as if the password policy is enforced for ‘sa’ or not.
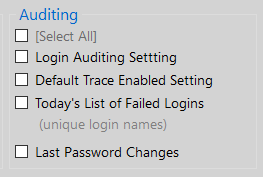
4.5 Auditing
This category features security checks related to auditing settings. It also provides other audit-related information.
Figure 4.6: ‘Auditing’ Security Check Group.
4.5.1 Login Auditing Setting
This check checks if the login auditing setting is set to both failed and successful logins or not.
4.5.2 Default Trace Enabled Setting
This check checks if the ‘Default Trace’ setting is enabled or not.
4.5.3 Today’s List of Failed Logins
This check returns the list with unique login names that failed during the day.
Note: If you run the credential checks (user:user, sa:sa) which are available in the Enterprise Edition of DBA Security Advisor, the reported failed login attempts will also include the connection attempts made by DBA Security Advisor during scanning for user:user and/or sa:sa. Please take this into consideration when reviewing this check’s findings. Also, the user:user check checks all SQL logins in the connectedSQL Server instance(s) except sa. ‘sa’ login can be checked with the ‘sa:sa’ check.
4.5.4 Last Password Changes
This check returns all logins whose passwords were not changed in the last 90 days.
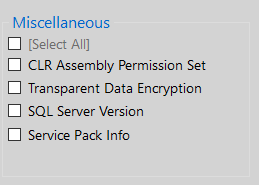
4.6 Miscellaneous
This category features different checks. Some of them have to do directly with security and some indirectly (i.e. service pack, etc.).
Figure 4.7: ‘Miscellaneous’ Security Check Group.
4.6.1 CLR Assembly Permission Set
This check reports all databases that have CLR assemblies registered with the ‘EXTERNAL_ACCESS’ or ‘UNSAFE_ACCESS’ permission set.
4.6.2 Transparent Data Encryption
This check reports all databases that are encrypted using Transparent Data Encryption (TDE).
4.6.3 SQL Server Version
This check reports the version of the connected SQL Server instances.
4.6.4 Service Pack Info
This check reports the installed service pack for the connected SQL Server instances.
4.7 Advanced
This category contains advanced checks.
Figure 4.8: ‘Advanced’ Security Check Group.
4.7.1 Database Engine Service Account
This check reports the service account for the database engine of the connected SQL Server instance(s).
4.7.2 SQL Agent Service Account
This check reports the service account for the SQL Agent engine of the connected instance(s).
4.7.3 Credentials Check (sa:sa)
This check checks if the password for the ‘sa’ login (if enabled) is the same with its name that is ‘sa’.
Note: Every time this check runs, in case the password is not the same as the login name, a failed login attempt will be added to the log. Please take this into when reviewing the findings of the Today’s List of Failed Logins check.
*Important Note 1: This check does not check different variations of the username as password (i.e. uppercase, lowercase, etc.). It just checks if the username, in the exact way as it is defined, is used also as a password for the specific login. This is done in order to avoid a potential lockout of the login.
*Important Note 2: Please take into consideration that if you run this check multiple times for the same instance, there is the risk of locking out the ‘sa’ login. To this end it is recommended to run it only one time per instance. If the ‘sa’ login is reported by the ‘Today’s List of Failed Logins’ check after running this check, then prior to running the sa:sa check again (in case you plan to), first log into the SQL Server instance via SQL Server Management studio using the ‘sa’ login, in order for the failed login times counter to reset.
4.7.4 Credentials Check (user:user)
This check checks if there are logins that have the same password the passwords as their name. ‘sa’ login is excluded from this check. If you want to check sa you can use the corresponding sa:sa check.
Note: Every time this check runs, in case the password is not the same as the login name (which is the recommended security practice), a failed login attempt will be added to the log. Please take this into when reviewing the findings of the Today’s List of Failed Logins check.
*Important Note 1: This check does not check different variations of the username as password (i.e. uppercase, lowercase, etc.). It just checks if the username, in the exact way as it is defined, is used also as a password for the specific login. This is done in order to avoid a potential lockout of the login.
*Important Note 2: Please take into consideration that if you run this check multiple times for the same instance, there is the risk of locking out the logins that might be reported to the ‘Today’s List of Failed Logins’. If this is the case, then prior to running the user:user check again (in case you plan to), first log into the SQL Server instance with the failed logins via SQL Server Management Studio in order for the failed login times counter to reset.
4.7.5 Latest DB Backup Times
This check reports the latest DB backup times for all the databases of the connected instances and raises a flag if a recent (within the two day) backup was not taken for a database.
4.7.6 BUILTIN\Administrators Access
This check checks if the BUILTIN\Administrators group has any server roles assigned.
5. Report
The report page presents the findings of all selected security checks that ran against the connected instances.
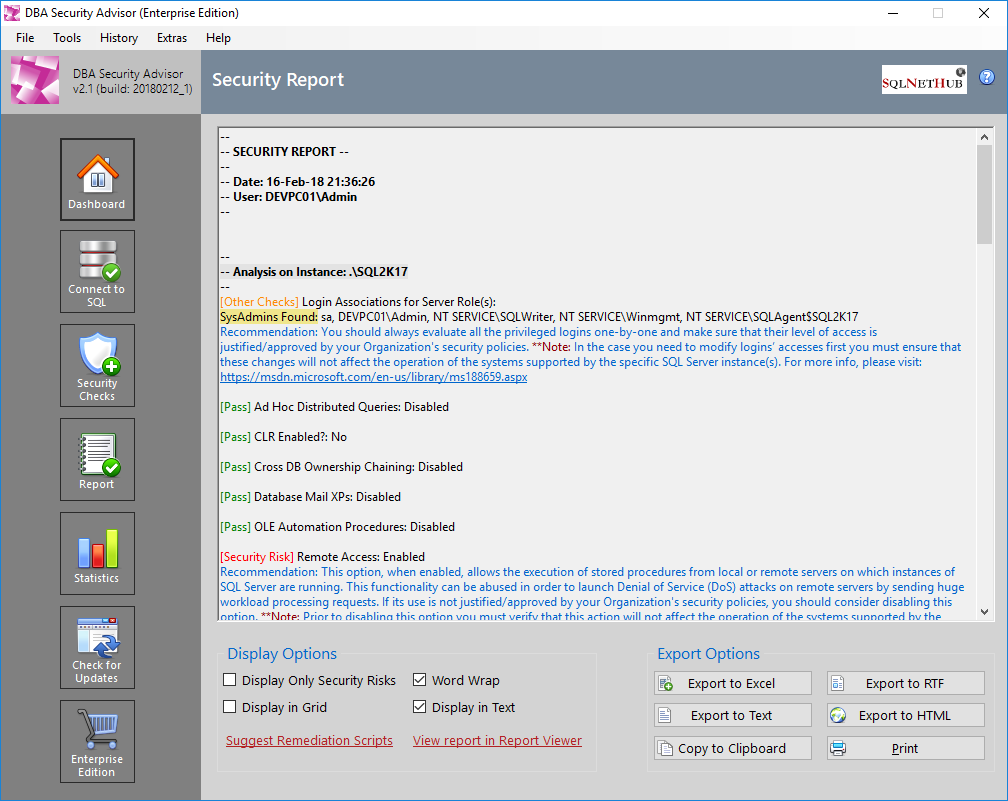
Figure 5.1: Embedded Report Viewer.
The security assessment findings are marked using the below flags, each flag with a different color:
[Pass]
[Security Risk]
[Other Checks]
The security checks that are marked with the flag [Pass] or [Security Risk] are scored checks.
The checks that are marked as [Other Checks] can be informational checks or general best practices checks and recommendations.
5.1 Display Options
Display options allow you to have different views of the security findings generated by DBA Security Advisor. For example, you can choose to view only security risks and display the report in text or grid format. Furthermore, if you are using the Enterprise Edition of the tool, you can have access to recommendations, scripts and suggestions for remediating the reported security risks. Additionally, you can view the report using the standalone Security Report Viewer.
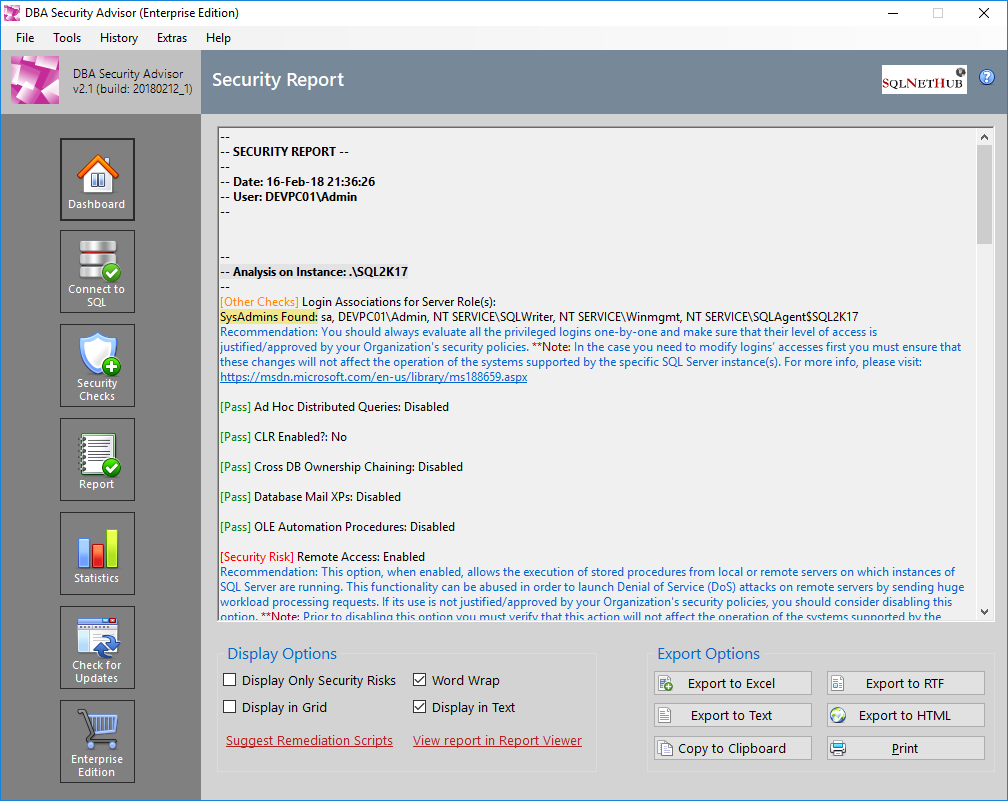
Figure 5.2: Display Options in Embedded Report Viewer.
5.2 Export Options
DBA Security Advisor provides a variety of export options. In the Free 7-Day Trial Version of the tool, you can copy the report to the clipboard as well as print it.
In the Enterprise Edition of the tool, in addition to the above, you can also export the report to Excel*, RTF, Text and HTML.
Figure 5.3: Export Options in Embedded Report Viewer.
*Note: You need to have Microsoft Excel 2010 or later installed on the same PC on which DBA Security Advisor is installed in order to be able to export to Excel.
5.3 View Report in Report Viewer
If you are using the Enterprise Edition of DBA Security Advisor, you can view the security report in the standalone Report Viewer thus reading it easier.
5.4 Suggest Remediation Scripts
One of the main benefits of DBA Security Advisor’s Enterprise Edition, is that you get recommendations for all detected security risks. Another benefit is that in addition to recommendations, you can request DBA Security Advisor to suggest remediation scripts and methods for the reported security risks.
6. Security Report Viewer
Security Report Viewer is another significant feature of DBA Security Advisor’s Enterprise Edition. In Security Report Viewer you can view the security report in full detail, including recommendations and remediation scripts. Additionally, it is used for displaying older reports via the Report History mechanism when is enabled (in Enterprise Edition).
Figure 6.1: Standalone Security Report Viewer.
6.1 Display Options
Display options allow you to have different views of the security findings generated by DBA Security Advisor. Additionally, you can get remediation scripts and methods by clicking on the “Suggest Remediation Scripts” link.
6.2 Export Options
In Security Report Viewer, you can export the displayed report using any of the below options:
Export to Excel*
Export to RTF
Export to Text
Export to HTML
Copy to Clipboard
Print
*Note: You need to have Microsoft Excel 2010 or later installed on the same PC on which DBA Security Advisor is installed in order to be able to export to Excel.
7. Tools
Under the ‘Tools’ menu category you can set different default options for DBA Security Advisor, as well as customize its appearance.
Figure 7.1: The ‘Tools’ Menu Items.
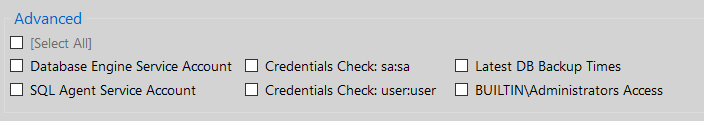
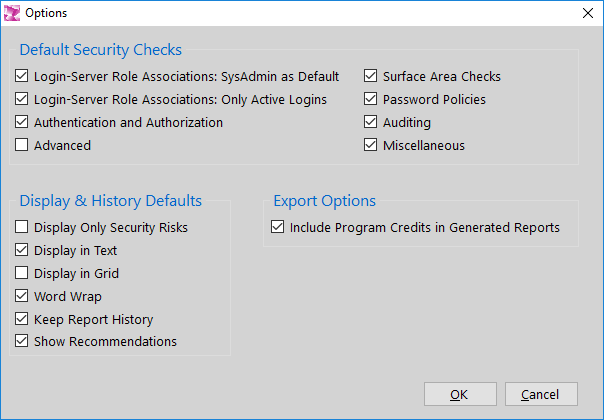
7.2 Options
Via Program Options you can set different default settings and preferences for DBA Security Advisor. Note that this is an Enterprise Edition feature.
Figure 7.3: Program Options.
The available options are:
Default Security Checks:
- Login-Server Role Associations: SysAdmin as Default
- Surface Area Checks
- Authentication and Authorization
- Password Policies
- Auditing
- Miscellaneous
- Advanced
Display & History Defaults:
- Display Only Security Risks
- Display in Text
- Display in Grid
- Word Wrap
- Keep Report History
- Show Recommendations
Export Options:
- Include Program Credits in Generated Reports
Miscellaneous:
- Show Start Page when Program Starts
8. History
History is another feature available in the Enterprise Edition of DBA Security Advisor. If DBA Security Advisor is set to keep history (by default is enabled – see Program Options for more info), then every time a report is generated, it is also stored on disk for future reference.
image
Figure 8.1: The ‘History’ Menu Items.
8.1 View Older Reports
As described above, if DBA Security Advisor is set to keep history, then with the ‘View Older Reports’ menu option, you can retrieve older reports and view them in Security Report Viewer. An interesting fact is that you can interact with the retrieved report, meaning that you can: choose to view only security risks or not, view remediation scripts, etc.
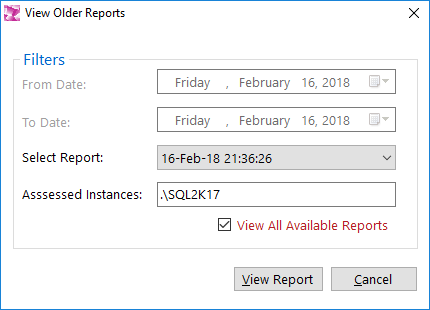
In order to retrieve an older report, you do not need to be connected to any SQL Server instances. You just need to select the old report by using the ‘View Older Reports’ dialog (see screenshot below).
Figure 8.2: Old Report Selector.
In the ‘View Older report’ dialog, you can search for older reports based on a date range search, or by just selecting the report to be retrieved from the list of all available reports. In order to assist you during the selection process, the assessed instances are presented every time you select a report to view.
8.2 Clear Report History
With this function you can clear the report history, meaning that any reports that have been previously generated and kept in history (given that the option to keep history was set to ‘on’) will be permanently deleted.
9. Extras
The ‘Extras’ menu provides two functions: (i) Connected Instance(s) Information, and (ii) Clear List of Recently Connected Instances.
9.1 Connected Instance(s) Information
This is another feature which is available in the Enterprise Edition of DBA Security Advisor. This function, when ran, will generate a report with important information about the connected SQL Server instances. For example, it will retrieve for each instance information such as: SQL Server version/service pack, edition, collation, etc.
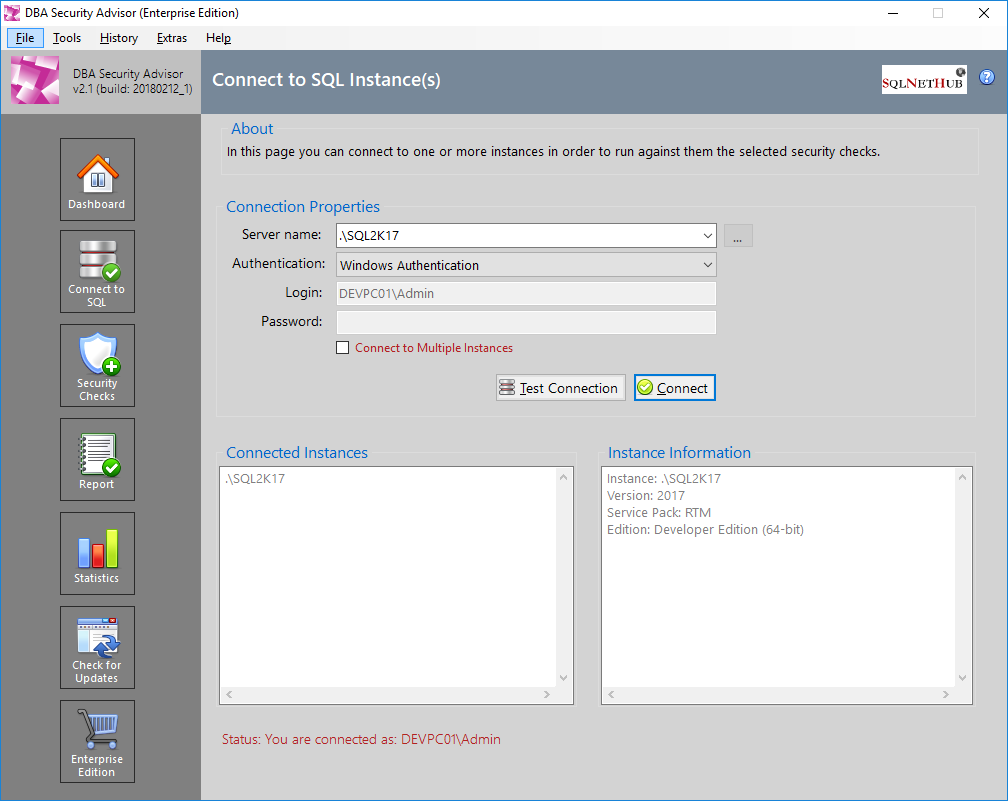
Figure 9.1: The ‘Connected Instance(s) Information’ Dialog.
The above report can be exported to:
Text file
RTF file
Clipboard
Printer
9.2 Clear List of Recently Connected Instances
With this function, you can clear DBA Security Advisor’s connected instances history.
10. Special Topics
This chapter features different special topics such as: the differences between the available editions of DBA Security Advisor, why upgrading to the Enterprise Edition, how to activate the Enterprise Edition after purchasing a license, etc.
10.1 Available Editions and Feature Comparison
DBA Security Advisor comes in two editions: (i) The Free 7-Day Trial Version which is free but has limited security checks and functionality and it expires after 30 days, and (ii) The Enterprise Edition where all security checks and features are available and there are no time limitations.
The below table compares the two DBA Security Advisor Editions.
| Feature | Free 7-Day Trial Version | Enterprise Edition |
| Time Limitation/Expiration | 30 Days | Unlimited |
| 7 Categories with more than 30 Security Checks:
Server-Level Accesses: o Logins – Server Role Associations Surface Area: o Ad Hoc Distributed Queries o CLR Enabled o Cross DB Ownership Chaining o Database Mail XPs o Ole Automation Procedures o Remote Access o Remote Admin Connections o Scan for Startup Procs o SQL Mail XPs o Trustworthy o SA Account Status o xp_cmdshell Authentication & Authorization o Server Authentication Mode o Guest User o Orphaned Users o Public Database Role o SA Account Check Password Policies o Password Expiration o Password Policy o Checks for SA (password expiration and policy) Auditing o Login Auditing Setting o Default Trace Enabled Setting o Today’s List of Failed Logins o Last Password Changes Miscellaneous o CLR Assembly Permission Set o Transparent Data Encryption o SQL Server Version o Service Pack Info Advanced o Database Engine Service Account o SQL Agent Service Account o Credentials Check (sa:sa) o Credentials Check (user:user) o Latest DB Backup Times o BUILTIN\Administrators Access
|
Only the Following Security Check Categories:
|
All Security Check Categories:
|
| Scan Single SQL Server Instance | ● | ● |
| Scan Multiple SQL Server Instances | ● | |
| Generate Security Report | ● | ● |
| Generate Recommendations for Security Risks | ● | |
| Generate Remediation Scripts for Security Risks | ● | |
| Security Report Display Options: Display Only Security Risks | ● | ● |
| Security Report Display Options: Word Wrap | ● | ● |
| Security Report Display Options: Display in Grid | ● | ● |
| Security Report Display Options: Display in Text | ● | ● |
| Security Report Display Options: Suggest Remediation Scripts | ● | |
| Security Report Display Options: View Report in Report Viewer | ● | |
| Security Report Export Options: Export to Excel
Note: You need to have Microsoft Excel 2010 or later installed on the same PC on which DBA Security advisor is installed in order to be able to export to Excel. |
● | |
| Security Report Export Options: Export to RTF | ● | |
| Security Report Export Options: Export to Text | ● | |
| Security Report Export Options: Export to HTML | ● | |
| Security Report Export Options: Copy to Clipboard | ● | ● |
| Security Report Export Options: Print | ● | ● |
| Program Customizations | ● | |
| Program Options | ● | |
| Report History | ● | |
| Informative Report On Connected Instance(s) | ● | ● |
| Connected Instances History | ● | ● |
Table 10.1: Features Comparison of DBA Security Advisor’s Editions.
10.2 Why Upgrading to the Enterprise Edition?
Data is the most valuable asset of every organization or individual. By the time you store your data in a Database Management System (DBMS), you need to take all the necessary steps in order to make it as secure as possible, in order to minimize as much as possible the risk of exposing your data to unauthorized third parties.
With the Enterprise Edition of DBA Security Advisor, you can assess your SQL Server instances against a rich set of security checks, get recommendations and remediation scripts, suggestions and information on how you can remediate potential security risks. As with all security tools, it would not be realistic to expect that by using DBA Security Advisor you will remediate all possible vulnerabilities on your SQL Server instance settings, but at least you will handle potential security risks identified by the rich set of security checks provided by the tool.
10.3 How Should You Use DBA Security Advisor
As mentioned in the previous subsection, it is not possible for a security tool to help you remediate all vulnerabilities on your SQL Server instances, because besides the instance configuration options and setup, there are different subsystems involved like: OS, network, storage, etc. which have their own setup and settings and thus potential vulnerabilities.
The hardening process for your SQL Server instances should be continuous on all levels, not only within your SQL Server instances but also on OS configuration, network security, storage permissions, etc.
DBA Security Advisor can be a part of this process, focusing on assessing the configuration of your SQL Server instances. You can use DBA Security Advisor to evaluate your SQL Server instances against the set of security checks provided in the tool and take corrective actions in the case where security risks are reported. It is recommended to frequently run DBA Security Advisor to ensure that for the provided security checks, no new risks were created due to possible misconfigurations or bad practices.
Activating the Enterprise Edition of DBA Security Advisor is very simple. After you purchase a license for the Enterprise Edition, the next step is to proceed with the activation. From within DBA Security Advisor, under the “Help” menu, you click on the “Activate Enterprise Edition” item:
Figure 10.1: The “Activate Enterprise Edition” Option.
You will then be presented with the Enterprise Edition activation dialog:
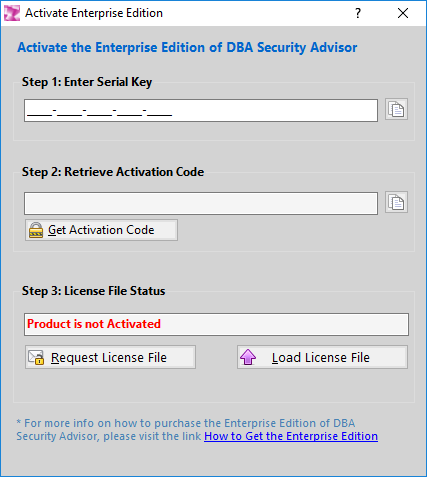
Figure 10.2: Enterprise Edition Activation Dialog.
In Step 1 of the activation process you need to enter the serial key that you were provided during your purchase of the Enterprise Edition license of DBA Security Advisor.
Next, by clicking on the “Get Activation Code” button you proceed to Step 2 where the activation dialog generates a unique hardware hash (a hash is a numeric value derived through a mathematical formula and based upon some other, original value) that is created by running 2 different pieces of information from the PC’s hardware components (BIOS id, Mainboard id) through a one-way mathematical transformation. This means that the resultant hash value cannot be backwards calculated to determine the original values and it ensures complete anonymity. This process was developed in order to maintain the user’s privacy and it is only used to deter software piracy.
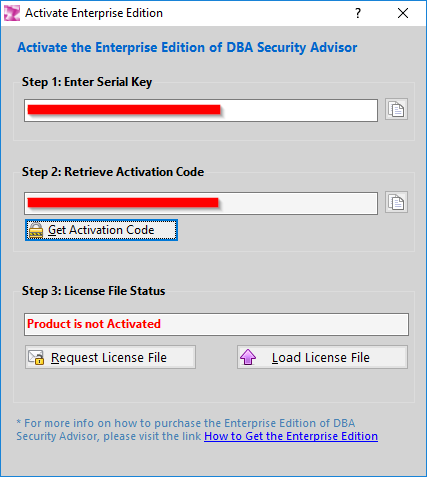
Figure 10.3: After Activation Steps 1 and 2 are Completed.
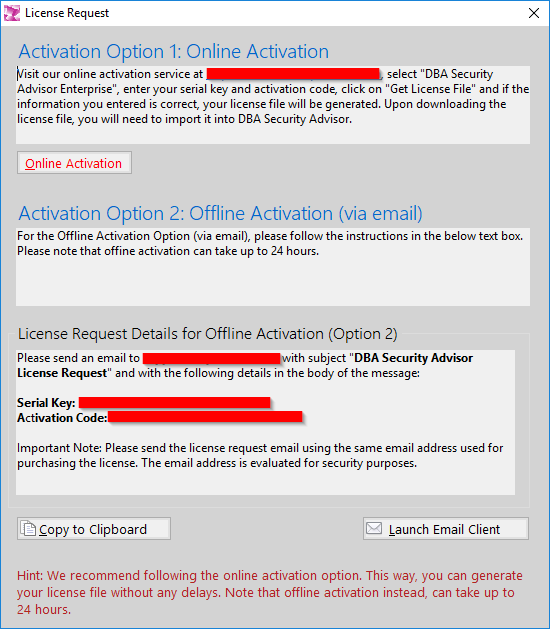
After steps 1 and 2 are completed, you can proceed to Step 3 which is requesting the License File. In this step you can click on the “Request License File” button and you will be presented with a message that needs to be sent to the DBA Security Advisor Licensing Service:
Figure 10.4: The License Request.
You can send the generated license request either by copying the serial key and activation code and sending it by email to the provided email address or by clicking on the “Launch Email Client” button and sending the dynamically created email (please use the same email address used for purchasing the license – this is done for security purposes) through your default email client.
After completing the license file request, if the submitted information is successfully validated, you will receive by email the license file which you can upload into DBA Security Advisor by clicking on the “Load License File” button. After this action, the Enterprise Edition of DBA Security Advisor will be activated.
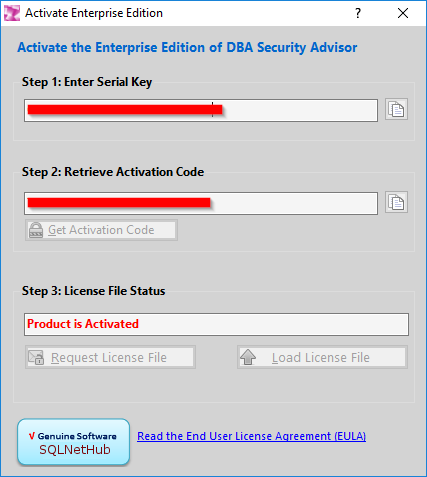
Figure 10.5: Successful Activation of the Enterprise Edition.
* Important Note: With a single license purchase of DBA Security Advisor’s Enterprise Edition you are allowed up to two (2) activations of the product for different hardware configurations. The second activation should be used in case your computer hardware was changed (i.e. mainboard) or even in the case you replaced your computer with a new one. In order to perform more than 2 activations for different hardware configurations you will need to purchase additional licenses.